Stop sharing plaintext secrets with your colleagues
Implement a secure way to share sensitive data within the Organization

Hrushikesh specializes in Application Security, Cloud and Cloud-Native security.
There are times when you have to share sensitive information with your colleague. It could be username/password to some dashboard or even to some database. It could be VPN credentials or even your Netflix password 🤷
Sharing the plaintext password through messaging applications, email, or even through Drive/Dropbox is not a good idea. Imagine someone getting access to your Organization's messaging application and finding plaintext passwords lying around along with some more sensitive and crucial information! Yikes!!! 🥴 That's something you would never want to see!
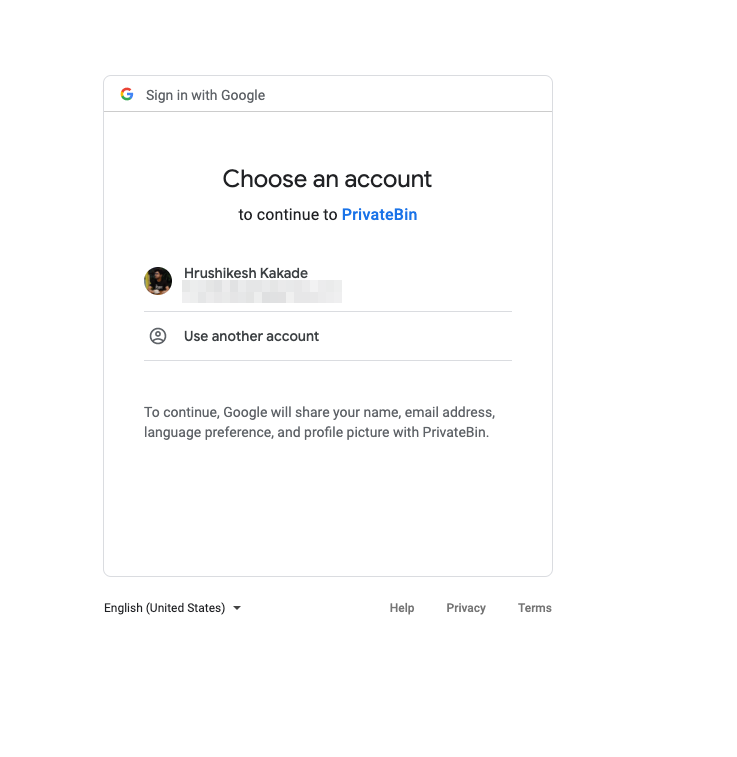
In this blog, we will learn how to set up a private secret sharing portal, that will be only available to the employees within your organization. The portal will be protected by Google Oauth and only the people having the Organization's email will be able to access it.
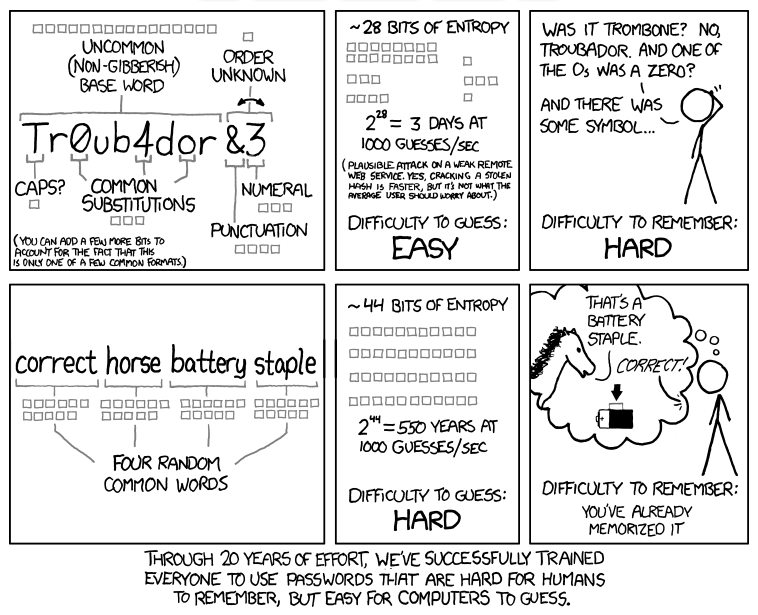 Source: xkcd comic
Source: xkcd comic
The Setup
To set up this portal we will be using the following components:
- Bitnami's OAuth2 Proxy to setup Google Authentication.
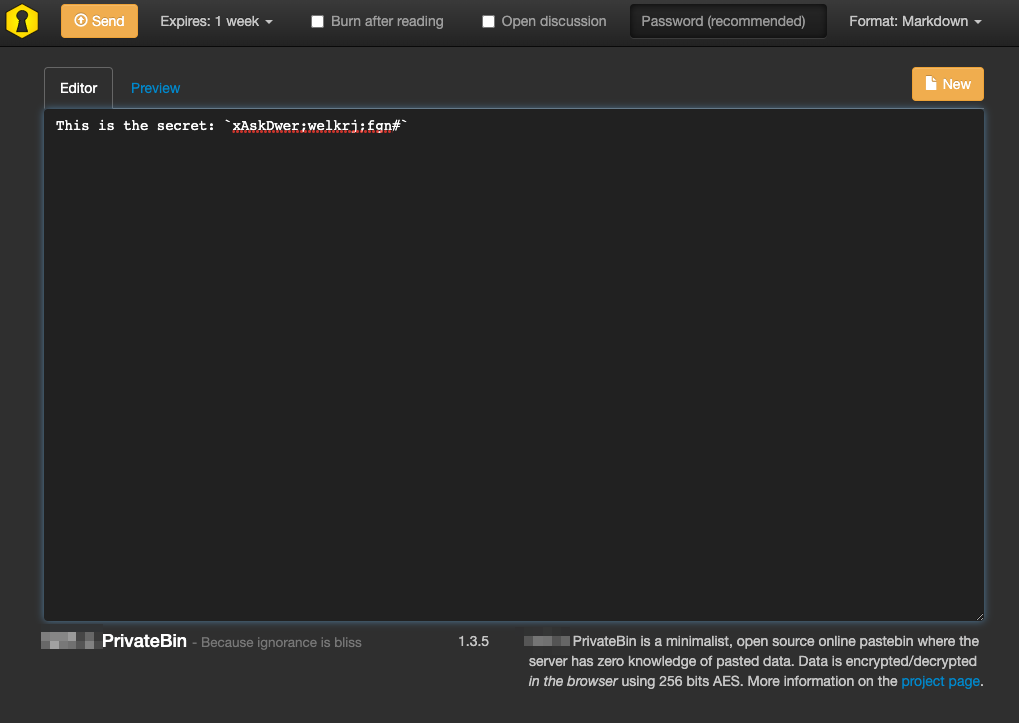
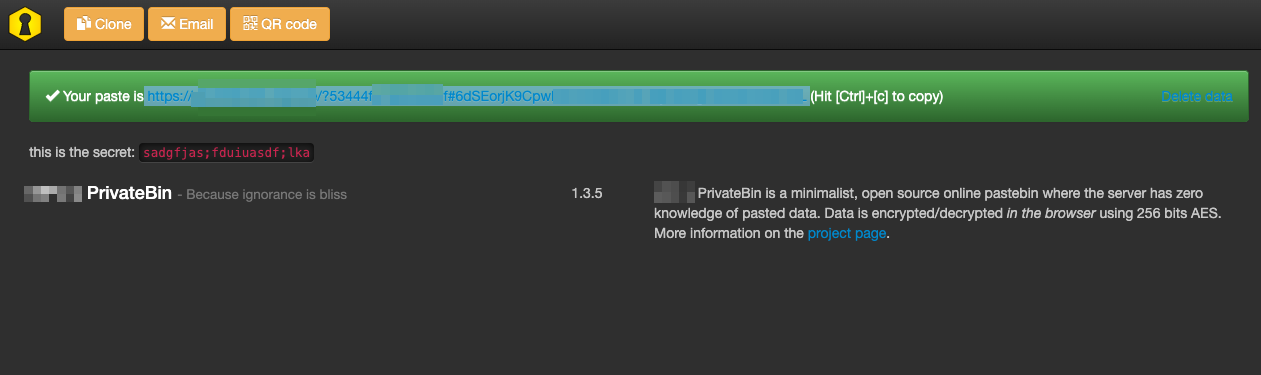
- PrivateBin as a secret sharing portal.
Google OAuth
First we will start by implementing Google OAuth. Follow this article to get the ClientID and ClientSecret
PrivateBin Portal
Before setting up the PrivateBin portal, make sure you have your Kubernetes Cluster up and running.
Next, once your nodes are up and running, install Nginx Ingress Controller using the following command:
kubectl apply -f https://raw.githubusercontent.com/kubernetes/ingress-nginx/controller-0.32.0/deploy/static/provider/aws/deploy.yaml
Create a namespace named privatebin. This is where PrivateBin and OAuth2 Proxy will be installed.
Next we will deploy Bitnami's OAuth2 Proxy using Helm Chart. OAuth2 proxy is required authenticate using the Google OAuth. Before installing the Helm Chart we will create file named oauth2.values.yaml to define some specific values.
config:
configFile: |-
email_domains = [ "example.com" ] # Your allowed email domains
upstreams = [ "file:///dev/null" ]
ingress:
enabled: true
path: /oauth2
hostname: privatebin.example.com. # Change
Make sure to change the domain to the domain that you are using. We can now install the OAuth2 Proxy's Helm chart with the following command:
helm repo add bitnami https://charts.bitnami.com/bitnami
helm install oauth2 bitnami/oauth2-proxy \
--values oauth2.values.yaml \
--namespace privatebin \
--set=configuration.clientID=${YOUR_CLIENT_ID} \
--set=configuration.clientSecret=${YOUR_CLIENT_SECRET} \
--set=configuration.cookieSecret=$(openssl rand -base64 32 | head -c 32 | base64)
This will install Kubernetes Objects required to Implement Google Authentication. Now we work on installing PrivateBin using Helm chart. Create a new file with the name privatebin.values.yaml and save the file with the following content:
# All requests to the PrivateBin should go through the oauth2-proxy
ingress:
enabled: true
annotations:
kubernetes.io/ingress.class: nginx
nginx.ingress.kubernetes.io/auth-url: "https://privatebin.example.com/oauth2/auth"
nginx.ingress.kubernetes.io/auth-signin: "https://privatebin.example.com/oauth2/start?rd=https://$host$request_uri$is_args$args"
cert-manager.io/cluster-issuer: "letsencrypt-prod"
tls:
- hosts:
- privatebin.example.com
secretName: privatebin-tls
hosts:
- host: privatebin.example.com
paths:
- path: "/"
configs:
conf.php: |-
<?php
; config file for PrivateBin
;
; An explanation of each setting can be find online at https://github.com/PrivateBin/PrivateBin/wiki/Configuration.
[main]
; (optional) set a project name to be displayed on the website
name = "Corporate's PrivateBin"
; enable or disable the password feature, defaults to true
password = true
; template to include, default is "bootstrap" (tpl/bootstrap.php)
template = "bootstrap-dark-page"
The statement cert-manager.io/cluster-issuer: "letsencrypt-prod" is needed if you're going to deploy Certmanager prod (which I highly recommend to).
To setup certmanager, follow this amazing blog by Digital Ocean.
Let's go ahead and install PrivateBin using Helm chart. Enter the following command:
helm install privatebin privatebin/privatebin \
--values privatebin.values.yaml \
--namespace privatebin
Conclusion
PrivateBin is now installed along with OAuth2 Proxy. The Ingress would've mapped to the Nginx Ingress Controller with a public IP. If you have setup Certmanager properly from the above blog then you can go ahead and visit the URL.



